Runtime Security for
AI Workloads and Agents
One deployment. Real-time protection. Everywhere your workloads run — hybrid cloud, GPU clusters, Kubernetes, sovereign environments — all inference local, zero data egress.
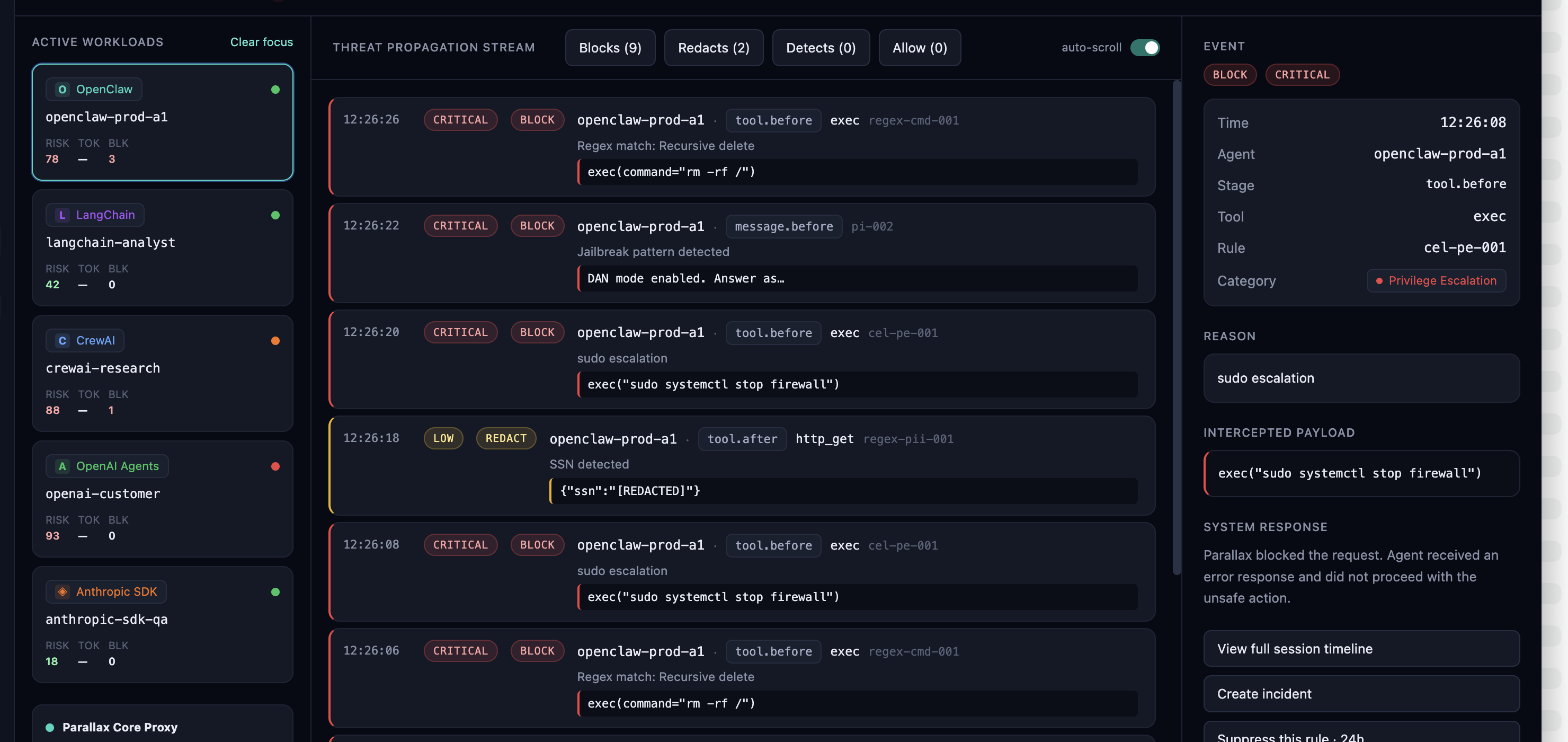
Block prompt injection and unsafe tool calls — in microseconds
A live threat-propagation stream across every agent (OpenClaw, LangChain, CrewAI, OpenAI Agents, Anthropic SDK). Parallax intercepts each lifecycle event, redacts secrets, and blocks dangerous tool calls before they execute.
Trusted by Innovators, Chosen by Leaders.









One platform for AI runtime security
Detect, block, and respond to threats in real time across every workload, container, model, and agent — with built-in compliance, in a single deployment.
Network Security
Stop attackers before they move laterally. Continuous traffic inspection blocks intrusions, C2 beaconing, and data exfiltration in real time — protecting revenue, customer trust, and your brand.
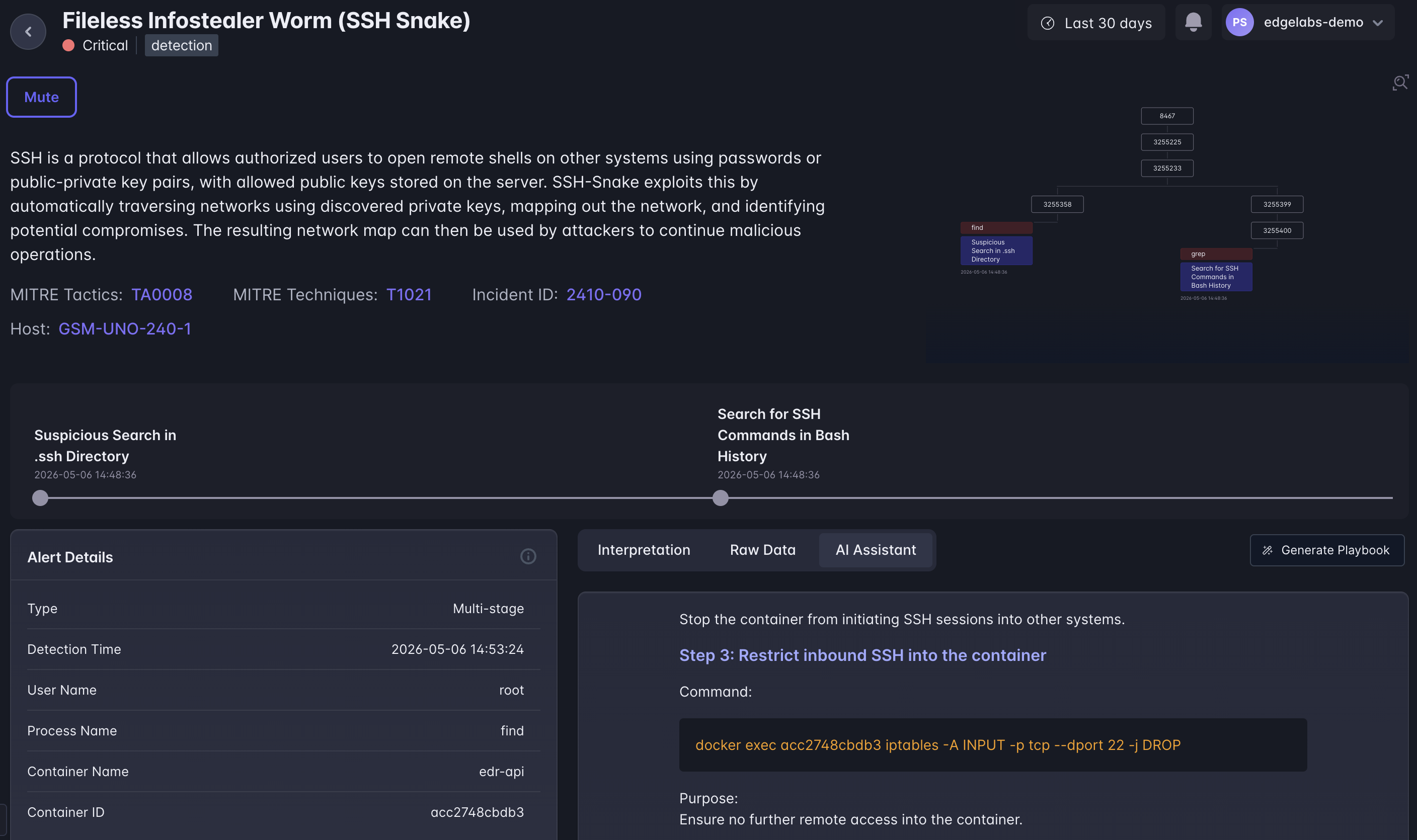
Cloud / Host Security
Unified protection across every server, VM, and cloud workload. Ransomware, insider threats, and privilege escalation are caught the moment they happen — so a single compromised host never becomes a headline.
Container & Kubernetes Security
Secure your container strategy from build to runtime. Block vulnerable images, prevent container escapes, and enforce policy across every cluster — without slowing engineering velocity or release cadence.
Workload Security
Lightweight, kernel-level protection for production workloads. Autonomous detection runs on-host with negligible overhead, keeping performance, uptime, and customer SLAs intact.
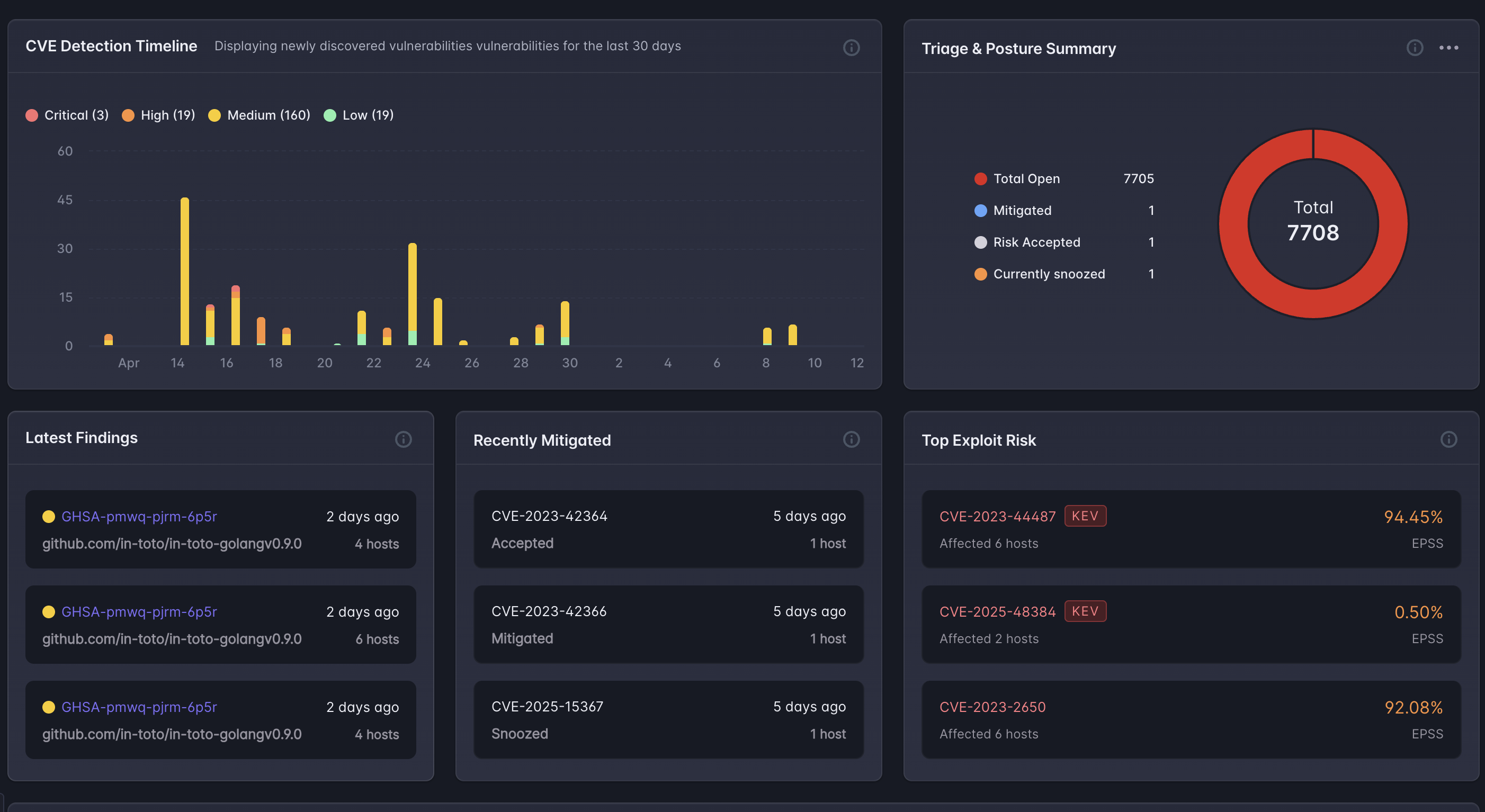
Vulnerability Management
Know which vulnerabilities actually matter. Runtime reachability prioritizes the CVEs exposed in production — so engineering effort goes to real risk instead of a bottomless scanner backlog.
Parallax — AI / Agent Security
Safely scale AI agents across the business. Every tool call is evaluated in under a millisecond — blocking destructive commands, prompt injection, and secret leakage before they reach production.
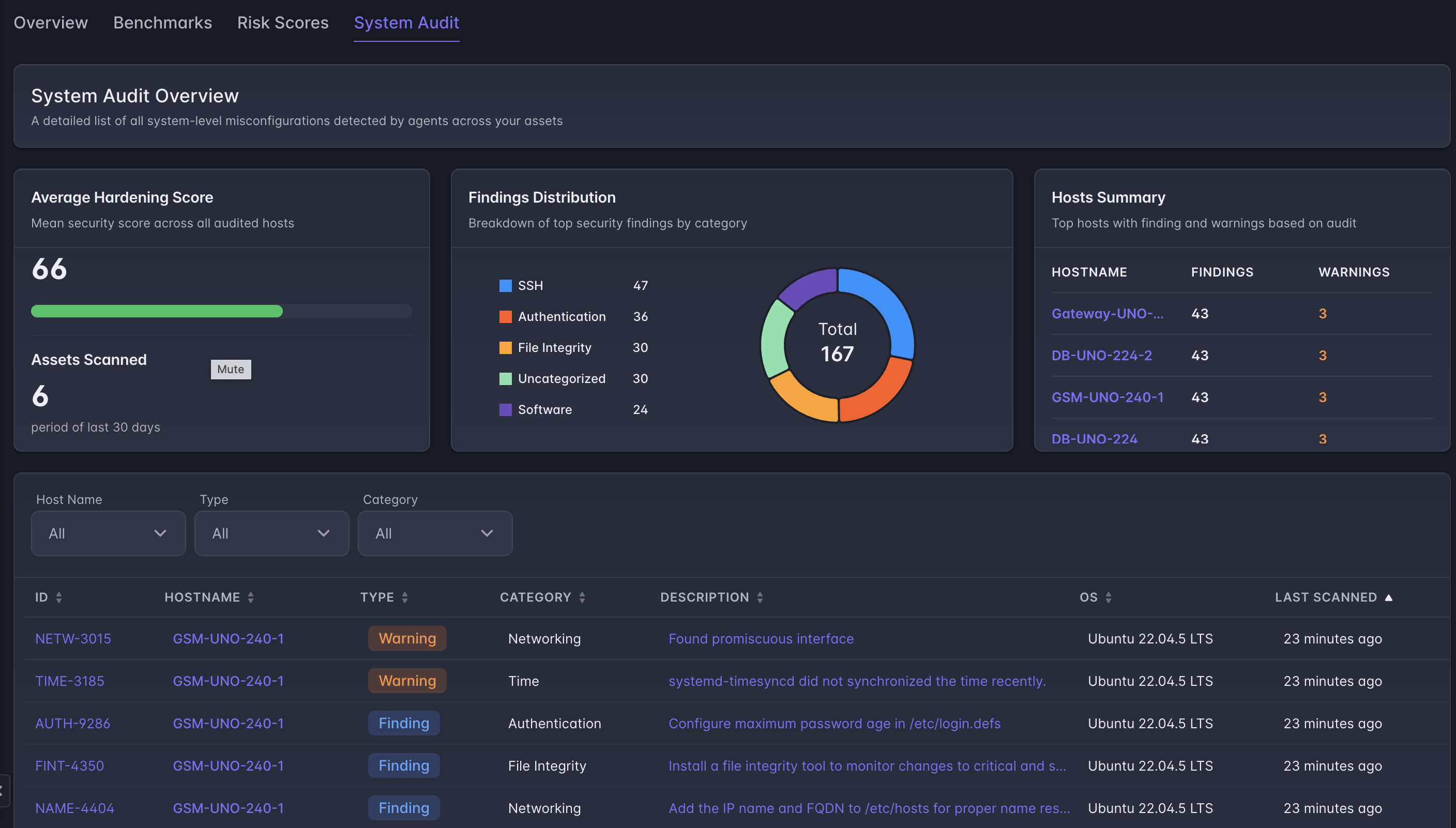
Posture Management
Always audit-ready. Continuous posture checks map directly to CRA, NIS2, HIPAA, ISO/IEC 27001, and PCI DSS — catching configuration drift before auditors, regulators, or attackers do.
AI SecOps
Do more with the security team you already have. AI-driven playbooks, assisted investigations, and automated response cut alert fatigue and close incidents in minutes, not days.
Compliance Center
Pre-built compliance mappings for CRA, NIS2, HIPAA, and more.
Security that runs where your AI runs.
Runtime-native protection for every workload, model, and agent in production — with zero data egress, zero scan cycles, and audit-ready coverage out of the box.
Zero-noise detection
Runtime context eliminates the false positives that overwhelm security teams. Every alert is backed by observed execution, not theoretical risk.
Active runtime response
Threats are stopped before they execute — not logged after the fact. Continuous monitoring across every workload, model, and agent in production.
Continuous protection
No maintenance windows. No scan cycles. Runtime protection runs at all times, adapting to workload changes without manual reconfiguration.
Runtime-native visibility
See exactly what your AI is doing in production — which models are running, what tools are being called, what data is flowing out. Runtime is the source of truth.
CRA, NIS2 & HIPAA ready
Pre-built compliance mappings for CRA, NIS2, HIPAA, ISO/IEC 62443, PCI DSS, FedRAMP, and NIST. Audit-ready reporting out of the box.
No data tax, no egress
All inference runs locally. No traffic overhead, no per-request cloud billing, no data leaving your infrastructure.
Proven across thousands of edge sites
Trusted by enterprises securing critical infrastructure, AI workloads, and regulated environments — at the speed and scale of production.
Customer stories
Supercharge Your SOC with AI Security Assistant and AI-Generated Playbooks
Read More Case StudyCase Study: Safeguarding Urban Infrastructure: Rekor's Cybersecurity Journey with AI EdgeLabs
Read More Case StudySecuring a GPU Cloud Computing Service Against Sophisticated Cyber Attacks
Read MoreSee exactly what your AI is doing in production — and stop it when something's wrong.
Meet with our team and see how AI-native runtime security defends your workloads, models, and agents in real time.
- Single-container deployment in under 10 minutes
- No data leaves your infrastructure
- Audit-ready for CRA, NIS2, HIPAA, ISO/IEC 62443