EPSS Scores. CISA KEV.
Vulnerabilities That Actually Matter.
Stop triaging by CVSS alone. EdgeLabs ranks every CVE by real-world exploit probability (EPSS), confirmed in-the-wild exploitation (CISA KEV), and internal fleet spread velocity — refreshed against vulnerability databases every hour. Prioritise what attackers are actually using, not what looks scary on paper.
Beyond CVSS — prioritise by real-world exploit risk
EdgeLabs integrates real-world exploitation signals to help prioritise remediation effort on the vulnerabilities most likely to be actively weaponised — not just those with the highest theoretical severity.
Exploitation-Rate Scoring
Go beyond CVSS — every CVE is scored with EPSS probability, CISA KEV status, and internal exploitation velocity to surface the vulnerabilities most likely to be weaponised.
Host Risk Scoring
Composite 0–100 risk score per host aggregating CVSS, EPSS, KEV presence, and fleet-spread velocity — weighted against each host's live network exposure surface.
Host Exposure Mapping
Enumerate every network-listening process, port, protocol, and user context on each host. Services bound to 0.0.0.0 or running as root are flagged for elevated exposure.
Container & System CVEs
Unified vulnerability detection across system packages and container images — with severity breakdown, affected package counts, and last-scanned timestamps per host.
Custom OS / SBOM Scanning
Upload CycloneDX or SPDX SBOMs for devices where agents can't run — embedded targets, OpenWrt, custom firmware. Full CVE coverage from build system or on-host export.
AI-Assisted Prioritisation
AI Assistant correlates CVE signals with runtime context to recommend which vulnerabilities to patch first — reducing triage time from hours to seconds.
End-to-end vulnerability detection pipeline
From agent-collected SBOMs to AI-assisted prioritisation — every step runs automatically and continuously across your entire fleet.
Host Agent
Collects installed packages, container images, and network exposure from every monitored host
SBOM Generation
Builds a Software Bill of Materials for system and container layers — or accepts manual SBOM uploads
CVE Database Scanning
Resolves components against NVD, OSV, and vendor advisory databases in real time
Exploitation Scoring
Applies EPSS, CISA KEV, and IEV signals — ranks every finding by real-world exploitability
AI Prioritisation
AI Assistant correlates signals and recommends fix order — reducing triage from hours to seconds
Three signals that separate noise from real risk
Each CVE detail view surfaces all signals — EPSS score, EPSS percentile, CISA KEV status, IEV, CVSS vector string, Exploitability Score, Impact Score, and CWE classification — in a single summary card.
EPSS (Exploit Prediction Scoring System)
A daily-updated probabilistic model from FIRST that estimates the likelihood of a CVE being exploited within the next 30 days. Both the raw score (0.0–1.0) and percentile rank across all CVEs are displayed on each finding.
CISA KEV (Known Exploited Vulnerabilities)
CVEs confirmed by CISA to have been exploited in the wild are flagged with a high-urgency badge and receive an automatic boost in the composite Risk Score — ensuring known-exploited findings are never buried in the backlog.
IEV (Internal Exploitation Velocity)
A platform-internal signal tracking how rapidly a given CVE is spreading across monitored assets in the account, highlighting vulnerabilities whose patch lag is creating a growing attack surface across your fleet.
Composite Risk Score — per host, per CVE
A composite Risk Score (0–100) is calculated per monitored host, aggregating the exploitation signals from all packages installed on the host and weighting them against the host's network exposure surface.
| Signal | Weight | Notes |
|---|---|---|
| CVSS Base Score (v3.1) | 30% | Normalised to 0–1 |
| EPSS Score | 35% | Daily exploit probability |
| CISA KEV Presence | 25% | Binary flag |
| IEV (Internal Velocity) | 10% | Normalised fleet-spread score |
Hosts are categorised as Low, Medium, High, or Critical based on their composite score. The exposure multiplier rises with the count and privilege level of network-listening services.
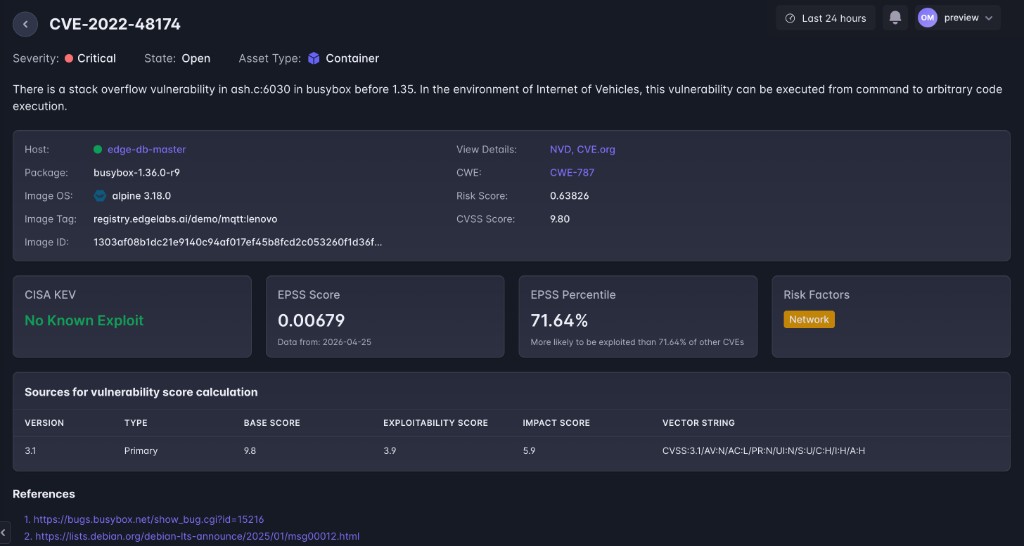 CVE detail view
CVE detail view
Full visibility across every host and container
The Vulnerabilities Overview dashboard gives security teams a single pane of glass across the entire fleet — with a CVE detection timeline, latest findings ranked by severity, and per-host vulnerability breakdown including affected packages, container images, and last-scanned timestamps.
- CVE Detection Timeline — newly discovered vulnerabilities over the last 30 days, colour-coded by severity
- Latest Findings feed — real-time list of newly detected CVEs with affected service and host count
- Per-host breakdown — system vulnerabilities, container vulnerabilities, affected packages and images at a glance
- Drill-down into System, Containers, Network, and SBOMs from the left-hand navigation
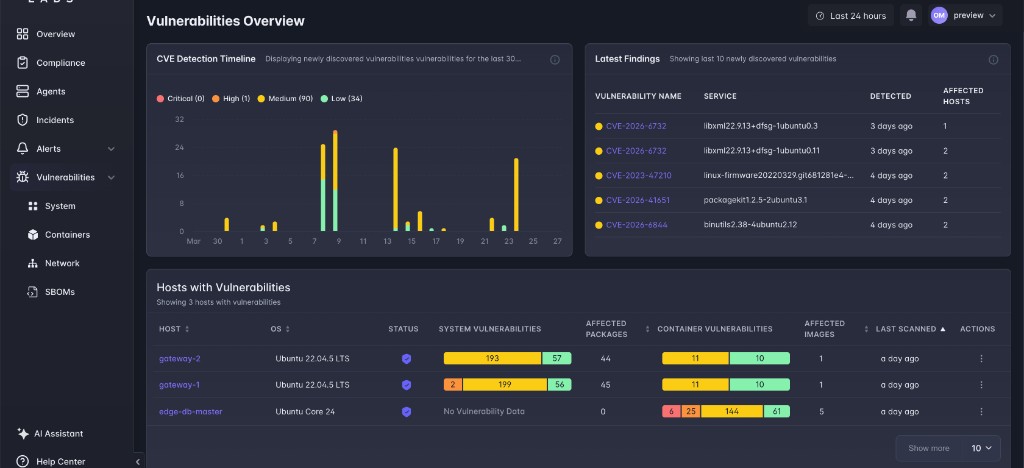 Vulnerabilities overview
Vulnerabilities overview
Map every listening service — surface real attack vectors
The Host Exposures view enumerates every process actively listening on a network port — including process name, port, protocol, listen address, user context, process state, and binary path. Services bound to 0.0.0.0 / :: or running as root are flagged for elevated exposure risk. This surface data feeds directly into the host risk calculation.
Process inventory
Every network-listening process, its PID, binary path, and owning user — captured in real time from the host.
Port & protocol mapping
TCP/UDP port, listen address, and protocol type — identifying services exposed to external traffic.
Privilege flagging
Services running as root or bound to 0.0.0.0 / :: are automatically flagged as elevated exposure.
Risk feed
Exposure data feeds the composite host risk score — more exposed services mean a higher multiplier.
CVE tracking for devices where agents can't run
For devices or operating systems where agent-based deployment is not feasible, EdgeLabs supports manual and automated SBOM (Software Bill of Materials) upload for vulnerability scanning — covering embedded targets, IoT gateways, and custom firmware.
Supported formats
CycloneDX JSON, CycloneDX XML, and SPDX 2.3 — up to 10 MB per file. Generated from the build system or on-host using tools like syft or the OpenWrt Image Builder SBOM export.
Automatic scanning
After upload the platform resolves each component against NVD, OSV, and vendor advisory databases and applies full EPSS / CISA KEV / IEV scoring — identical to agent-based findings.
Differential scanning
Successive uploads for the same asset highlight newly introduced or remediated vulnerabilities between builds — giving engineering teams clear upgrade guidance.
Fix version guidance
Where a patched version exists it is displayed alongside the vulnerable version — so teams know exactly which upgrade resolves each CVE.
Custom OS support
Full CVE coverage for embedded targets such as OpenWrt, Yocto, and custom Linux distributions — generated from the build system or on-host.
API access
All SBOM operations — upload, list, retrieve findings — are available via the REST API for CI/CD pipeline integration and build-time vulnerability gates.
EPSS percentiles. CISA KEV flags. Hourly DB updates. Deployed in minutes.
Stop triaging thousands of CVEs by severity alone. Deploy EdgeLabs and let real-world exploit signals — EPSS scores, KEV confirmations, and fleet-wide velocity — tell your team exactly what to patch first.