AI/LLM Security
Full visibility. Guardrails enforcing.
When language becomes code, ambiguity becomes risk. AI EdgeLabs gives you a clear view into AI agent runtime activity, prevents agents from running dangerous operations, and enforces your rules locally — not relying on the LLM provider to do the right thing.
Take back control of AI agent runtime
AI EdgeLabs builds full agent defense on top of the open-source Parallax evaluator engine — intercepting every message and tool call at four lifecycle stages, running them through a cost-ordered chain of five evaluator engines (regex, pattern, Sigma, CEL, SQL temporal), and acting in under 0.2 ms. Add fleet-wide discovery, behavioural drift, shadow-AI detection, and DLP correlation across every host you already run AIEL on.
External Guardrail Enforcement
LLM-side guardrails are recommendations the model can ignore. AIEL enforces guardrails outside the model — every tool call, command, and output is checked against your policy before it executes.
Activity Graph & Perimeter Fence
Live visibility into what every agent is actually doing — domains hit, processes spawned, tools called, files touched. Draw a perimeter fence around an agent and block anything stepping outside.
Shadow AI Detection
Continuously observe hosts and network traffic for unauthorized AI agents and LLM endpoints — including ones standing up silos of sensitive data outside CTO/CISO/COO oversight.
Data-Loss Prevention (DLP)
Automatic detection and redaction of secrets, credentials, PII, and sensitive context before they reach a third-party LLM, are written to disk, or are sent to another tool.
Native Agent Integration
Drop-in integration with Claude Code, Codex, OpenClaw, LangChain, CrewAI, and the OpenAI/Anthropic SDKs — or run as a transparent proxy between agent and provider with zero code changes.
Behavioral Drift Detection
Each LLM execution is non-deterministic. AIEL learns each agent's normal operating scope and flags suspicious divergence — recursive deletes, new outbound domains, escalation attempts, model overrides.
Full agent defense on top of Parallax
The same concentric defense model that wraps your workloads now wraps every LLM tool call. Parallax sits inline with each agent and enforces policy in microseconds; AI EdgeLabs adds discovery, behavioural baselines, fleet posture, and audit-grade correlation across every host — turning a single-binary evaluator into a full agentic-security control plane.
Cost-ordered evaluator chain
Regex, keyword pattern, Sigma rules, CEL expressions, and SQL-based temporal analysis run in cost order, cheapest first. The chain short-circuits the moment any rule returns block — layered defense without paying for it on every call.
Lifecycle interception
Hook into message.before, tool.before, tool.after, and params.before. Every prompt the model sees, every tool it tries to call, every result returned, and every parameter forwarded — inspected before execution, every time.
Microsecond decisions
Single static Rust binary, zero runtime dependencies — no Python, no JVM, no containers required. Typical decisions complete in under 0.2 ms; agents don't feel the inspection, attackers don't get the window.
Integrate any way you ship
Server mode exposes POST /evaluate for any framework that speaks HTTP. Proxy mode drops in front of Anthropic or OpenAI APIs and evaluates every request, response, and streaming tool call — with zero code changes.
Rollout — five stages from deploy to compliance
Why AI agents need external security
LLM-powered agents introduce an entirely new risk surface. Language is non-deterministic. Guardrails are suggestions. And agents operate faster than any human can observe.
Guardrails are just recommendations
Execution guardrails inserted into LLM configs are soft suggestions — models can and do ignore them. Just 9 seconds were needed to delete a production database. External enforcement is the only way to guarantee compliance.
Non-deterministic execution
Every agent execution can produce different results. Language is non-deterministic, and so is the outcome. Teams need monitoring for suspicious divergence from the agent's standard operational scope.
Limited observability
Agents make decisions and execute fast — there's no room for humans to observe it all. Organizations need a clear view into agent operations: domains contacted, processes spawned, resources consumed.
Shadow AI proliferation
AI agents can ease everyday operations but introduce decentralized risk — separate locations of sensitive information and vulnerabilities outside traditional CTO/CISO/COO department structures.
Real-time fleet posture for every AI agent
See every agent across your fleet at a glance — which frameworks they run (OpenClaw, LangChain, CrewAI, OpenAI Agents, Anthropic SDK), their protection state, risk score, active rule coverage, and the latest blocks and detections.
- Blocked attacks, redacted egress, and suspicious events — in real time
- Latest blocks feed with severity, rule ID, and description
- Top threat categories with 24-hour trending (prompt injection, dangerous commands, data exfiltration, PII, reconnaissance)
- Per-agent risk score, rule coverage, and gap analysis
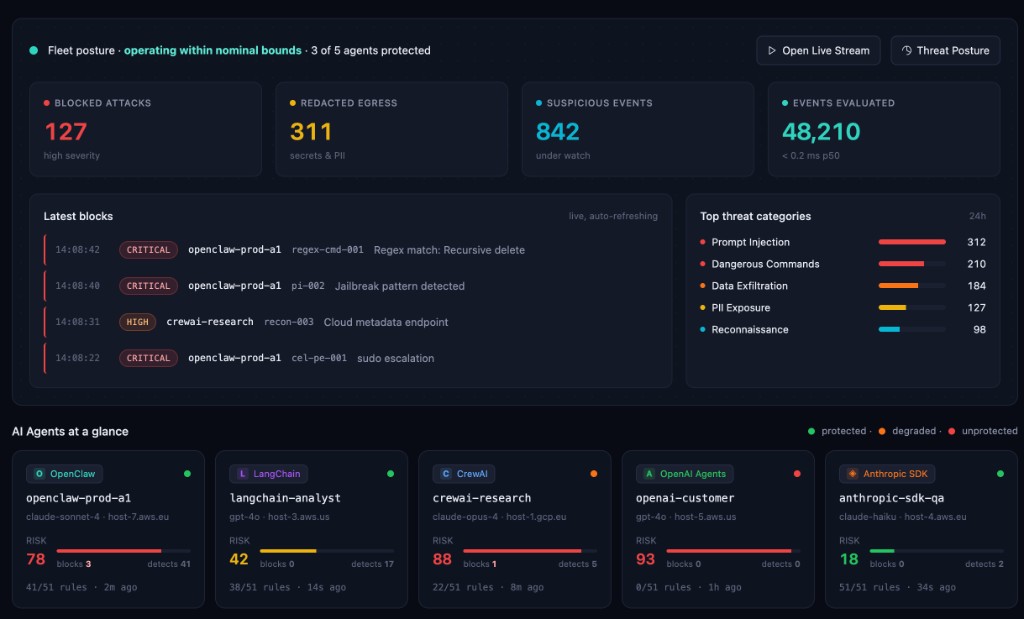 Fleet Posture
Fleet Posture
Defense coverage across the fleet
Each row shows which Parallax evaluators are active per agent. Instantly spot missing coverage and surface it as a vulnerability — before attackers do.
- Evaluator types: prompt-injection guard, dangerous commands, privilege escalation, PII scanner, secret scanner, rate limits
- Hook-point visibility:
message.before,tool.before,tool.after - Status indicators: nominal, high load / risk, critical anomaly
- Rule coverage and gap counts per agent
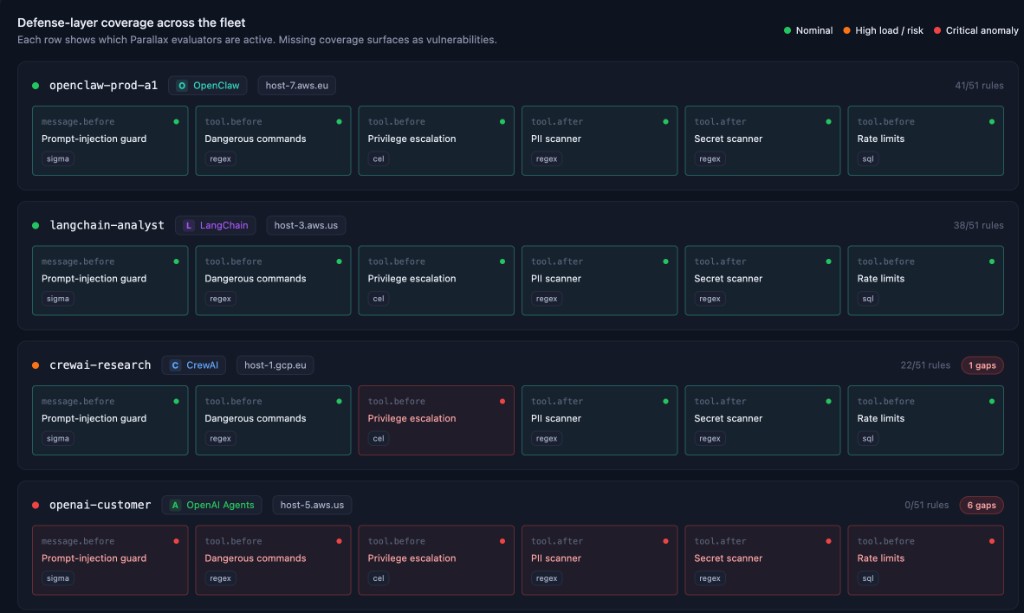 Defense Coverage
Defense Coverage
51 rules across 13 categories
Parallax evaluates every tool call against a comprehensive, configurable rule set. All rules ship out of the box and are fully customizable.
See what your AI agents are really doing — and enforce the rules that matter.
Deploy external guardrails, detect shadow AI, and prevent data loss across your AI fleet. One platform. Full runtime visibility. Sub-millisecond enforcement.